✅ Last checked on
What if the secret to crystal-clear video calls and instant messaging lies in a protocol you’ve never heard of? This text-based system quietly powers over 90% of internet-based communication today, yet most users don’t realize how it shapes their daily interactions.
The technology behind today’s voice and video connections acts like a digital traffic controller. It establishes sessions between devices, negotiates capabilities, and manages connections from start to finish. Unlike older phone systems, this approach uses familiar web protocols to enable real-time conversations across any internet-connected device.
You’ll find this framework at work in business phone networks, mobile LTE calls, and even gaming voice chats. Its flexibility comes from using plain text commands – similar to how websites load content – making it easier to integrate with other tools. Combined with security protocols like TLS encryption, it creates reliable connections while protecting sensitive data.
Key Takeaways
- Standardized method for starting and ending voice/video sessions
- Works with HTTP-like text commands for easy integration
- Supports business phone systems and mobile LTE networks
- Uses companion protocols for media handling and security
- Enables features like call forwarding and conference bridging
What is SIP (Session Initiation Protocol)?
Your video chats depend on an unseen protocol orchestrating each session. This text-based system acts as a digital handshake that starts, manages, and ends multimedia exchanges. Unlike traditional phone networks, it uses familiar web-like commands to connect devices across any internet connection.
Definition and Purpose
The protocol establishes rules for devices to find and recognize each other. Think of it as a multilingual translator that helps different systems agree on how to share voice, video, or chat data. Its main job is setting up sessions – not carrying the actual media streams.
Key Features
You get three core strengths with this approach. First, it works with plain text messages for easy troubleshooting. Second, it supports instant session modifications like adding participants mid-call. Third, it integrates with security layers to protect your conversations.
Relationship to Other Communication Protocols
The system teams up with specialized partners to handle different tasks. Session Description Protocol (SDP) defines technical details like video resolution in the background. Real-time Transport Protocol (RTP) then delivers the actual voice/video packets once the handshake completes.
Transport flexibility makes it adaptable to various networks. Whether using UDP for speed, TCP for reliability, or SCTP for advanced features, the protocol maintains consistent performance. This layered approach follows internet standards while allowing future upgrades.
The History and Evolution of SIP
Behind every modern video conference lies an unexpected origin story. The protocol emerged in 1996 from internet engineers seeking better ways to connect devices. Unlike traditional telecom systems, this framework was built for flexibility rather than rigid voice networks.
Origins and Development
Early web pioneers developed the first version to handle multimedia sessions over IP networks. The Internet Engineering Task Force (IETF) adopted it in 1999 through RFC 2543. This marked a shift from telephone company-controlled standards to open internet-driven solutions.
Mobile networks embraced the technology in 2000 when 3GPP added it to their architecture. This decision laid groundwork for today’s LTE voice services and video streaming apps. The approach prioritized text-based commands familiar to web developers over binary telecom formats.
Standardization Process
June 2002 brought the pivotal RFC 3261 update. This revision fixed early limitations and established core features still used today. The IETF continues refining the specification through extensions addressing security and new media types.
Traditional protocols like H.323 followed closed telecom development models. In contrast, this framework grew through open collaboration. Public feedback and real-world testing shaped its evolution, enabling rapid adoption across diverse platforms.
How SIP Works: Protocol Operation
Imagine building a conversation layer by layer. The protocol coordinates connections through a precise sequence of text-based instructions. These messages handle session creation first, then manage ongoing interactions, and finally terminate connections.
Basic Call Flow
Your device starts with an invitation message. A response confirms availability. Media channels open only after both parties agree on technical details. This handshake prevents compatibility issues during data transfer.
SIP Addressing and URI Format
Contacts use email-like addresses with special prefixes. This format works across devices and networks. You might recognize patterns like sip:user@domain.com in technical settings.
Transport Layer Options
Messages travel via UDP for speed or TCP for reliability. Encrypted versions use TLS for security. The system adapts to network conditions automatically.
Interaction with Other Protocols
Session Description Protocol (SDP) handles media specifics like codecs. Real-time Transport Protocol (RTP) carries voice/video packets separately. Security layers like SRTP protect content without disrupting flow.
This layered approach explains why multiple protocols appear in call logs. While SIP manages connections, other systems handle media quality and encryption. The number of cooperating protocols ensures flexibility across different communication tools.
Essential Network Elements in SIP Architecture
Behind every seamless call between devices lies a hidden network framework. This infrastructure connects different communication technologies while maintaining security and reliability. Four core components work together to make this possible.
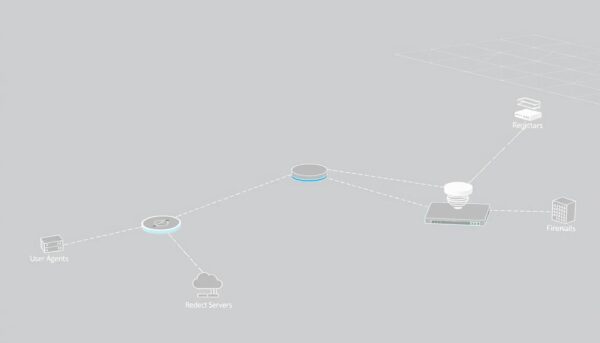
User Agents
Your devices act as communication endpoints. Smartphones and computers use software to send and receive session requests. These tools handle both initiating calls (client mode) and responding to them (server mode).
Proxy Servers
Digital traffic directors route your requests through the network. They verify identities and determine the fastest path for data. Some proxies add encryption layers to protect sensitive information during transit.
Registrars and Redirect Servers
A central database tracks active devices on the system. When you move between networks, these servers update your location details. Redirect tools help reroute calls when primary paths become unavailable.
Gateways and Session Border Controllers
Specialized bridges connect modern IP networks with legacy phone lines. This lets you call landlines from internet-based services. Session Border Controllers (SBCs) act as security checkpoints with three key functions:
| Component | Primary Role | Protocol Handling |
|---|---|---|
| Gateways | Protocol translation | SIP ↔ PSTN |
| SBCs | Security enforcement | SIP/RTP optimization |
“True interoperability requires both technical bridges and policy alignment between service providers.”
SBCs handle firewall challenges and encrypt media streams. They enable secure network configurations while maintaining call quality. These components ensure your video conferences work across different platforms and internet connections.
Understanding SIP Messages and Transactions
Ever wonder how your video call recovers when network errors strike? The answer lies in structured message exchanges that keep conversations flowing smoothly. These text-based instructions handle everything from connection attempts to error recovery.
Request Types
Devices exchange seven core commands to manage sessions. INVITE starts conversations, while BYE ends them. ACK confirms successful connections, and CANCEL stops pending requests. Other types handle mid-call adjustments and status checks.
Response Codes
You’ll encounter three categories of replies during calls:
- Provisional (1xx): “Trying” or “Ringing” updates
- Success (2xx): Connection established
- Errors (4xx-6xx): Failed attempts with specific reasons
Transaction Management
The protocol uses timers to prevent frozen connections. A typical exchange follows these steps:
- Device sends request
- Recipient responds within 32 seconds
- Automatic retries if no reply
- Session cleanup after completion
| Transaction Type | Duration | Key Feature |
|---|---|---|
| INVITE | Minutes-hours | Creates dialogs |
| Non-INVITE | Seconds | Single exchanges |
“True reliability requires both immediate responses and long-term session tracking.”
Dialogs maintain ongoing call context through unique identifiers. This system ensures your device remembers active sessions even when switching networks. Multiple transactions can occur within one dialog, enabling features like call transfers.
Real-World Applications of SIP
Your daily communication tools rely on hidden infrastructure that connects voice, video, and text seamlessly. This protocol powers more than phone calls – it creates unified systems where multiple formats work together. Below are three key areas where these capabilities shine.
Voice Communication Systems
Businesses save 40-80% on call costs using internet-based phone services. These systems handle international calls through SIP-based systems instead of traditional lines. Features like auto-attendants and CRM integration make customer interactions smoother.
Group Video Solutions
Modern meeting platforms scale from 1:1 chats to 500+ participant webinars. The protocol adapts bandwidth usage based on network conditions. See how it compares to older methods:
| Feature | Traditional | SIP-Based |
|---|---|---|
| Scalability | Limited hardware | Cloud expansion |
| Cost | Per-user licenses | Flat-rate sips |
| Features | Basic video | Screen sharing + recording |
Messaging & Availability Tools
SIMPLE extensions turn the protocol into a chat powerhouse. You see colleagues’ statuses before calling – green for available, red for busy. MSRP adds file transfers without leaving the conversation window. These sips-enhanced tools often replace standalone messaging apps in corporate environments.
Unified platforms combine all three functions into single interfaces. This integration reduces app switching and improves response times. Your communication stack becomes more efficient without sacrificing capabilities.
SIP Security and Encryption
Security remains a top priority for internet-based communications. Modern systems use layered protections to safeguard both call setup processes and media streams. The SIPS URI scheme acts as your first defense, requiring TLS encryption for all signaling traffic. Addresses like sips:user@example.com ensure every handshake between devices gets secured before media flows.
Two critical shields protect your conversations. TLS wraps signaling data like caller IDs and routing details. SRTP then encrypts voice/video packets during transfer. This dual-layer approach stops eavesdroppers from intercepting sensitive information.
Challenges emerge when calls pass through multiple servers. While SIPS secures each connection point, true end-to-end encryption requires direct device links. Enterprise solutions often combine TLS with VPNs or IPSec tunnels for added protection across networks.
| Security Layer | Protocol | Protection Scope |
|---|---|---|
| Signaling | TLS | Call setup data |
| Media | SRTP | Voice/video content |
| Authentication | MD5 | User verification |
Best practices demand strict certificate management and port configurations. Always use port 5061 for encrypted traffic instead of default 5060. Regular audits help maintain secure connections without sacrificing call quality or features like conference bridging.
Conclusion: The Future of SIP in Communication Technology
As digital conversations evolve, one standard quietly shapes their foundation. The protocol discussed throughout this article bridges traditional telephony and modern internet-based systems, proving its value across decades of technological shifts. Developed through open collaboration, it continues adapting to new demands while maintaining backward compatibility.
Emerging trends reveal its long-term potential. Integration with 5G networks enhances mobile communication reliability, while IoT devices leverage its flexibility for smart environments. AI-powered features like voice assistants and real-time translation demonstrate how the protocol evolves alongside cutting-edge tools.
Challenges remain in security and cross-platform compatibility. However, the framework’s text-based design simplifies updates and extensions. This adaptability explains why businesses increasingly adopt it for unified communications – reducing costs while improving collaboration.
The result of its open standards approach? Widespread innovation without vendor lock-in. As augmented reality and WebRTC gain traction, this foundation ensures seamless integration. While newer protocols may emerge, its role in shaping global communication infrastructure remains secure for the foreseeable future.